Магазин
В інтернет-магазині компанії Ви можете купити вимірювальні прилади в Україні, ціна яких є найнижчою. У нас представлені лише надійні та продуктивні прилади від лідерів цього сегменту ринку. Оперативна доставка, бездоганний сервіс, зручні засоби плати, кваліфікована допомога при виборі! Опис приладів від професіоналів пошукайте на сайті ango.org.ua.
Для оформлення замовлення на вимірювальні прилади зв’яжіться з нашими операторами за телефоном +38 097 919 41 91.
Ну, а поки ви чекаєте, коли наші менеджера Вам передзвонять, погортайте блог https://sop.org.ua/.
Отображение единичного результата.
-

Термоанемометр ALT-866
5,581грн. В корзину -

Термоанемометр ALT 31
7,155грн. В корзину -
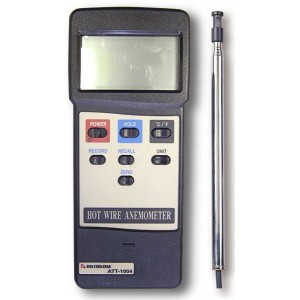
Анемометр АТТ-1004
10,876грн. В корзину -

Цифровой анемометр CV-321
1,603грн. В корзину -

Универсальный прибор LM-8000A (Анемометр, люксметр, гигро, термометр)
4,579грн. В корзину -

Анемометр DT-318
4,579грн. В корзину -

Анемометр CV-320
5,724грн. В корзину -

Анемометр ИС 2
7,298грн. В корзину -

Виброметр цифровой CV-65A
8,255грн. В корзину -

Виброметр AR63С
6,296грн. В корзину -
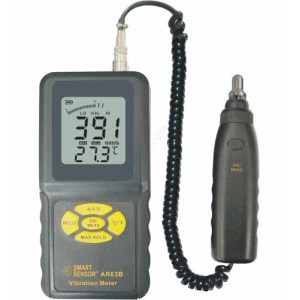
Виброметр AR63B
8,557грн. В корзину -

Виброметр AR63A
4,579грн. В корзину -

Индикатор-виброметр подшипников ИДП-07
13,881грн. В корзину -

Цифровой профессиональный виброметр Fluke-805
47,223грн. В корзину -

Виброметр Vibro Vision
4,579грн. В корзину -

Виброметр 107В
23,755грн. В корзину